- by gowthamk91
Introduction
Azure AD B2C custom policies are used to handle complex scenarios for user flow. Default user flows (sign up, sign in, password reset, and edit profile) will fulfill the basic requirements. However, if you need more customization in the flow based on the business requirements, the custom policies will come into the picture. The custom policies are XML-formatted files, it is fully configurable and policy-driven.
Most complex scenarios with custom policies are documented, and the source code is available on GitHub. In this series of Azure B2C custom policies, you will learn how to start with the starter pack and then the complex business scenarios that I came across on my Azure ADB2C custom policy assignments.
Pre-Requisites
- Azure ADB2C Tenant
- Basic Knowledge in XML
Get Start with Azure ADB2C Custom Policies
Click here to download the Azure AD B2C Custom Policies starter pack.
Extract the folder and go to LocalAccounts. There will be different folders like SocialAccounts, SocialAndLocalAccounts, and many more, but in this series, I will cover all the scenarios only with LocalAccounts.
Open the LocalAccounts folder in VS code or Visual Studio.
List of files
- TrustFrameWorkBase – This is a base file for the development (Don’t do any update in this file)
- TrustFrameworkLocalization – This file has all the localization elements, if you need to make changes in default messages in the flow, this file will help you.
- TrustFrameworkExtensions – The extension file is where most of the configuration changes will happen.
- SignUpOrSignin.xml, ProfileEdit.xml, PasswordReset.xml – These are the Relying party files called by the application to initiate the respective flow.
Hierarchy of AD B2C Custom Policies

Register Web Applications
IdentityExperienceFramework
Step 1: Sign in to Azure portal and Switch to Azure B2C tenant.
Step 2: Go to the overview page, select Identity Experience Framework, and select App Registrations.

Step 3: Click on New Registration and provide the name as Identity Experience Framework

In Supported account types, select Accounts in this organizational directory only (tenant name B2C only – Single tenant).
Under Redirect URIs, select the type as Web and the value should be https://tenant-name.b2clogin.com/tenant-name.onmicrosoft.com
Note: Replace the tenant-name with your tenant’s name in the URI.
Step 4: In the Permissions section, select the Grant admin consent to openid and offline_access permissions check box and click on Register.

Step 5: Select the Expose an API from Manage blade, under Edit application ID URI check the Application ID URI, and click on Save.


Step 6: Click on Add a scope from the same screen. Enter the following details.
Scope name – “user_impersonation”
Admin consent display name – IdentityExperienceFramework
Admin consent description – Allow the application to access IdentityExperienceFramework on behalf of the signed-in user.


Step 7: Click on Add scope to save a setting.
ProxyIdentityExperienceFramework
Step 1: Click on App registrations from the Manage blade, click on new registration, and name it ProxyIdentityExperienceFramework.
Step 2: In Supported account types, select Accounts in this organizational directory only.
Step 3: From the Redirect URI section, use the drop-down to select public client/native (mobile & desktop), and for Redirect URI, type myapp://auth.
Step 4: From the Permissions section, select the Grant admin consent to openid and offline_access permissions check box. Click on register to Save.

Step 5: Select the API permissions from Manage Blade and Select IdentityExperienceFramework app from the APIs my organization uses.

From the select permissions section, select the user_impersonation scope and select the Add permissions button.
Step 6: Finally, select Grant admin consent for (tenant name).
Signing Key
- Go to Identity Experience Framework and click on Policy Key.
- Select Add, create a key pane will be opened.

- In Name, enter TokenSigningKeyContainer , it will be prefixed wil B2C_1A_ after the creation
The TokenSigning key container is essential for Azure Active Directory B2C applications within the Identity Experience Framework. It facilitates trust between applications and the Microsoft identity platform by utilizing public-key cryptography to sign security tokens containing user information. This container securely stores the private key used by the Microsoft identity platform for token signing.
The Microsoft identity platform exposes the public key in the tenant’s OpenID Connect discovery document or SAML/WS-Fed federation metadata document. Applications utilize this key to verify the signature of tokens. It’s crucial to be aware that the Microsoft identity platform periodically rotates its signing key, necessitating applications to handle key rollover events, regardless of frequency.
- Select RSA from key type field
- Select Signature from Key usage field
- Click on create
Encryption Key
- Go to Identity Experience Framework and click on Policy Key.
- Select Add, create a key pane will be opened
- In Name, enter TokenEncryptionKeyContainer , it will be prefixed wil B2C_1A_ after the creation

“The TokenEncryption key container in the Identity Experience Framework plays a vital role in securing tokens by encrypting and decrypting sensitive information like user identity and access permissions. Upon installation, the Identity Experience Framework automatically establishes a TokenEncryption key container to securely store the encryption key needed for this protection.”
- Select RSA from key type field
- Select Encryption from Key usage field
- Click on create.
Update the custom policy files
Update the tenantname in all the custom policies files.
Wherever you find the “yourtenant” replace it with your tenant’s name.
Open TrustFrameworkExtensions.xml
Locate<Metadata> replace ProxyIdentityExperienceFrameworkAppId with ProxyIdentityExperienceFramework application Id.
Locate<Metadata> replace IdentityExperienceFrameworkAppIdwith IdentityExperienceFrameworkAppId application Id.
Upload Custom Policy files
Go to Identity Experience Framework and click on Upload custom policy.

Upload the custom policies by following sequences.
- TrustFrameworkBase
- TrustFrameworkLocalization
- TrustFrameworkExtensions
Other files (SignUp_SignIn, ProfileEdit, PasswordReset) can be uploaded on any sequence.
Uploaded files
By default, the policy name prefixed with B2C_1A_

Test the Flow
Register a new application to test the flow,
Click on App registration and select new registration. In my case, I named it as FlowTest

Name – FlowTest
Supported account types – Accounts in any identity provider or organizational directory (for authenticating users with user flows)
Redirect URI – Web – https://jwt.ms
Check Grant admin consent to openid and offline_access permissions.
Click on Register to register the application. After the registration select authentication from Manage Blade and select Access Tokens and ID tokens and click on save.

Go to Identity Experience Framework and select B2C_1A_SIGNUP_SIGNIN flow.
Select B2C_1A_SIGNUP_SIGNIN flow

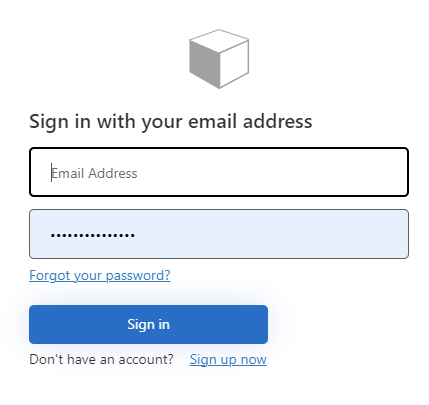
Select the application created to test the flow and click on Run now. You can see the login screen, and from there you can click Sign up now to register.

Complete the registration. After the registration, you will be redirected to jwt.ms site, where you can check decoded tokens and claims.
Summary:
We have seen what is Azure ADB2C custom policies, how to get started and configure using Azure portal and finally, we have tested the user flow using Azure portal. We are going to see more about custom policies in my future articles.