- by gowthamk91
Introduction:
The Azure application proxy supports single sign-on access to the application that uses SAML, Header, Kerberos, and Password-based SSO. In this article, we are going to see how to leverage the header-based SSO in the Azure application proxy. I highly recommend you check my article on Azure application proxy before getting into it.
Header-based SSO:
We already installed an Azure app proxy connector and successfully established a remote connection between the client and internal on-premise applications in my last article.
Now, let’s integrate the header-based SSO.
Step 1: Log in to the Azure portal and go to Enterprise applications
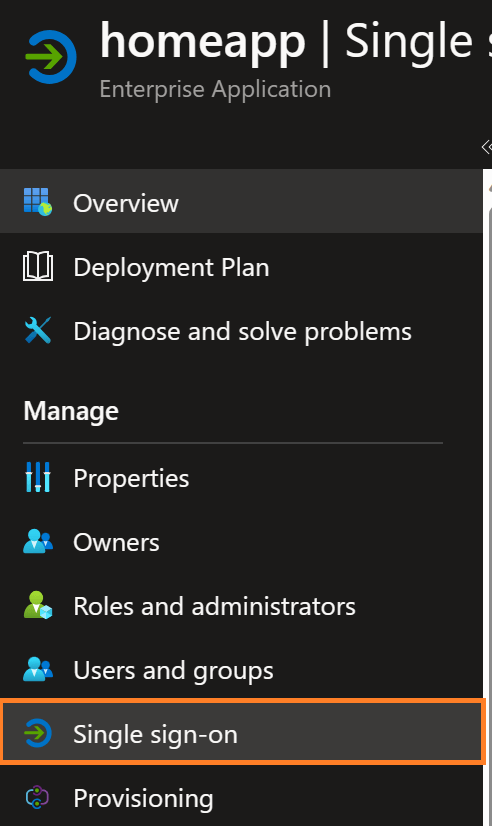
Step 2: Select the application “homeapp” which we created in the last article.
Step 3: Select Single sign-on from Manage Blade and select header-based.

Step 4: Keep the Azure active directory option for the configure field from the select mode section.
Step 5: Click on the Edit button in Configure Headers section, click on Add new header, and select the attribute to be passed through the header as claims. After validating the token, the application proxy service will read these claims from the token and send it as an HTTP header request to the connector, and the connector will send this information to the internal application in a header request.



Step 6: Save the header configuration

Step 7: Test the application and check header details. I have hosted the .NET 6 web application on the premise that will pull all the header details from the HTTP request.
Run the application in my case the external URL is https://homeapp-gowthamk91outlook.msappproxy.net/

As we expected we got a userprincipalname from the header request. If your applications are developed with header-based SSO functionality you can leverage these features from Azure active directory application proxy
Summary:
We have seen how to configure the header-based single sign-on with the Azure application proxy and how to add the header attributes that can be used by the application for authorizing the user. We will see more features on the Azure application proxy in my next article.